Open-source projects play a key role in technological advancement and community development, which is why we at Viris also strive to contribute our share. In this article, we present how we enhanced the open-source tool Responder by adding support for the MQTT protocol, which is also widely used in smart home automation.
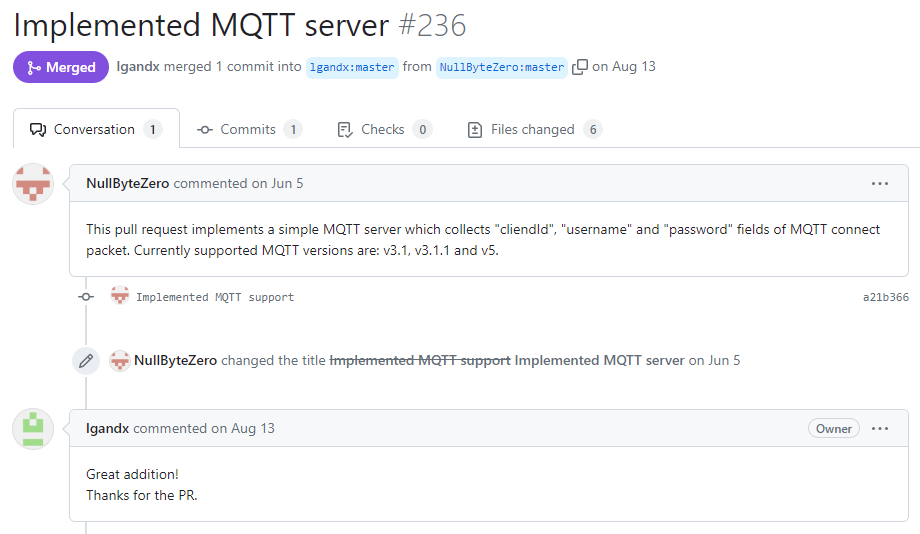
Our contribution to the Responder project was merged into the main branch on August 13, 2023
(https://github.com/lgandx/Responder/pull/236)
What is MQTT?
If you have ever worked with smart home automation or connected a larger number of sensors into a centralized system, you have most likely already heard of the MQTT protocol.
MQTT (Message Queuing Telemetry Transport) is a lightweight messaging protocol based on the publisher–subscriber communication model. It was designed for telemetry and similar applications where efficient, low-overhead data exchange is required, often in network environments with limited resources or unreliable connectivity.
The protocol is widely used in Internet of Things (IoT) applications, as it enables communication between a large number of devices while maintaining low power consumption and broad connectivity. Due to its simplicity and efficiency, MQTT is also popular in industrial environments where reliable communication between devices is essential.
Despite its widespread adoption, MQTT introduces certain security risks, especially when communication is not properly secured. Without encryption, an attacker may not only intercept messages exchanged between publishers and subscribers but may also forge or modify them, creating a serious security vulnerability.
Improving Security Through Practical Experimentation
As part of an experiment focused on the configuration of the Eclipse Mosquitto server, we explored the security landscape of MQTT in greater depth. Our objective was to capture MQTT credentials transmitted over unsecured connections.
To achieve this, we focused on enhancing Responder. While the tool already supports DNS poisoning and a wide range of network protocols, it originally lacked compatibility with MQTT. We therefore developed our own extension.
We added MQTT server support on port 1883, enabling Responder to analyze each incoming connection. It detects the protocol version (v3.1, v3.1.1, or v5) and extracts key information from the packets, such as the hostname, username, and password. This enhancement not only strengthened Responder’s capabilities but also provided deeper and more detailed insight into potential vulnerabilities.
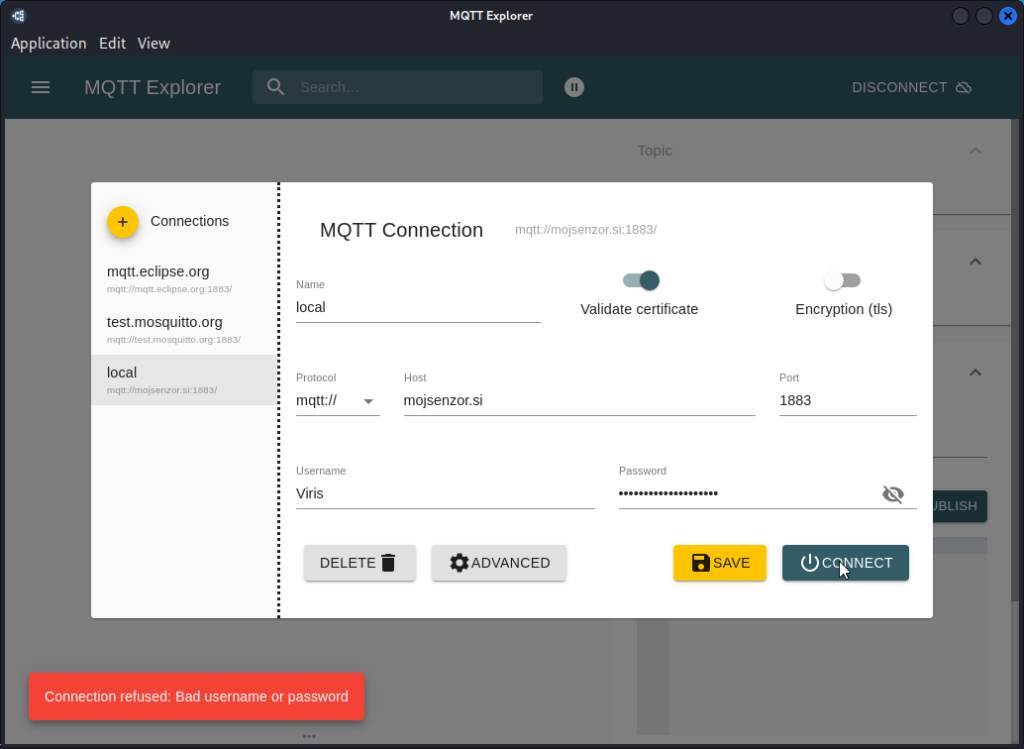
The image below shows an example connection attempt to the fictional domain “mojsenzor.si.”
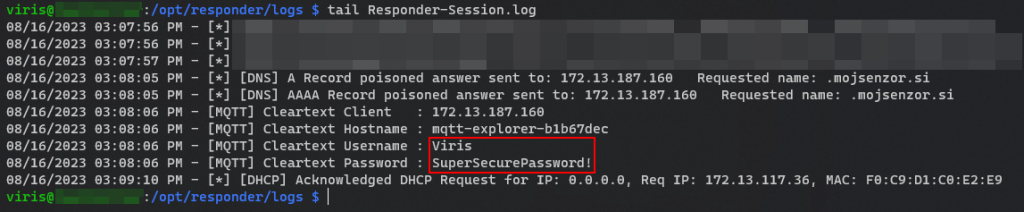
By examining the Responder-Session.log file, we can see that the previously entered credentials were successfully captured.
For example, imagine a building where wireless thermometers are used to monitor temperature and humidity, transmitting their data over the MQTT protocol. The system is configured so that, in the event of a fire (detected by a rise in temperature), it triggers an alarm and automatically unlocks all secured doors. A potential attacker could use Responder together with our extension to capture the credentials of a temperature sensor and send falsified sensor readings to the server, triggering the alarm and thereby enabling unauthorized access to the building. If the electronic door locks themselves also communicated via MQTT, the attacker could potentially gain entry without triggering any alarm at all.
In today’s digital age, as technology continues to evolve, open-source projects foster collaboration and accelerate innovation. Contributing to such projects is more than technical participation—it reflects a commitment to transparency, cooperation, and the advancement of the broader community. That is why we are proud to contribute to the open-source ecosystem, believing that together we can help build a safer and more innovative world.