Are you an enthusiast interested in the rapidly developing world of cybersecurity? With the increasing use of information technologies and the internet, cyberattacks have become more frequent and sophisticated. Demand for skilled cybersecurity professionals is growing, making it the right time to start your career in this exciting field. This article will guide you through the steps and help you on your journey into cyberspace.
Develop a solid foundation in computing
To succeed in the field of cybersecurity, you need a foundation in computing concepts. Start by following trends, news, and current events in the computing world. Focus on areas such as networks, programming, and operating systems, and for math enthusiasts, cryptography.
Get involved in the cybersecurity community
Networking plays a crucial role in advancing your knowledge. Join cyber communities to connect with people who have similar interests. Attend conferences, workshops, and webinars to stay current with the latest trends. Engaging in these communities will help you gain additional knowledge.
One of the more popular conferences is BSides, an excellent source for acquiring knowledge and connecting with other cybersecurity professionals. These conferences are organized worldwide, where experts share their experiences and knowledge and present the latest research in the field (https://0x7e7.bsidesljubljana.si/).
Students can join local university communities, such as:
- Hack Club FERI (https://hackklub.feri.um.si/) and
- DragonSec SI (https://dragonsec.si/)
Use learning and training platforms
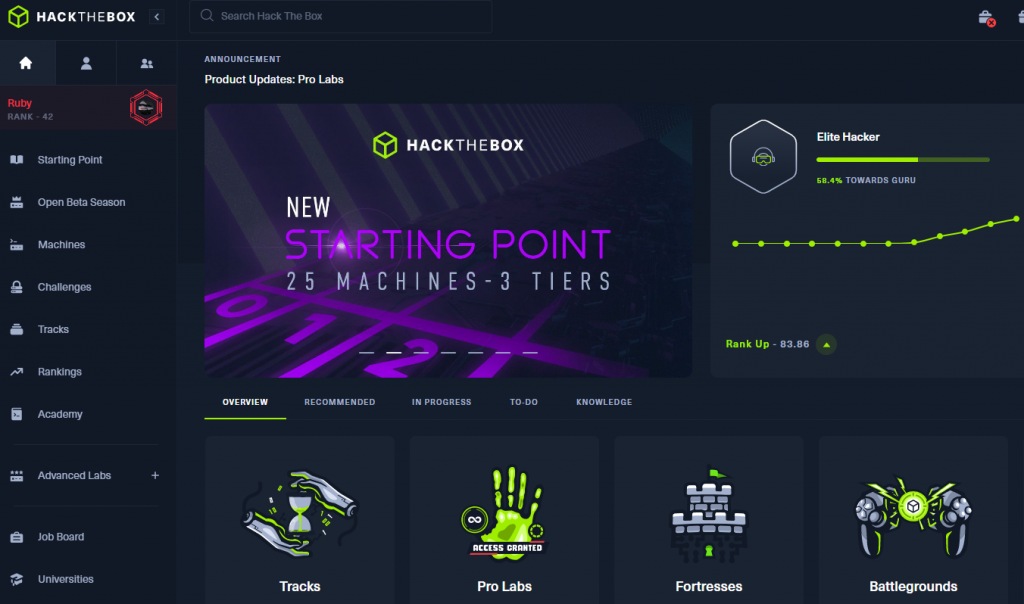
Take advantage of online platforms such as HackTheBox Academy, TryHackMe, and OverTheWire, which offer a range of challenges and courses for beginners and experts who want to improve their skills and knowledge in cybersecurity. On these platforms, you can perform security tests on virtual systems, learn about different techniques and tools, and upgrade your knowledge.
HackTheBox Academy (https://academy.hackthebox.com/) is a platform that provides realistic problem-solving scenarios and opportunities to participate in Capture The Flag competitions.
TryHackMe (https://tryhackme.com/) offers a wide range of learning paths covering various aspects of cybersecurity, from basics to advanced concepts.
OverTheWire (https://overthewire.org/wargames/) is another popular platform that offers a set of challenges for learning different aspects of computer security.
By regularly participating on these platforms, you will improve your skills, gain valuable experience, and be better prepared for the challenges this field brings.
Test your skills in competitions
Test your abilities in cybersecurity competitions, such as Capture The Flag (CTF) events. These competitions challenge you to solve real cyber problems and allow you to learn from others in a fun and competitive environment. Participating in such events will sharpen your problem-solving skills and demonstrate your passion for cybersecurity to potential employers. A list of upcoming competitions can be found at https://ctftime.org/.
Main categories in CTF competitions
🕸️ Web: Web category includes web challenges that test your knowledge of web application operation, common vulnerabilities, and misconfigurations. The flag is hidden somewhere in the web application, and you reach it by exploiting logical or technical flaws in the web application. The most common web application vulnerabilities are described in OWASP Top 10 (https://owasp.org/www-project-top-ten/).
⚙ Reversing: The reverse engineering category mainly involves the analysis of devices, programs, and processes. Reversing requires a good understanding of Assembly language and processor architecture. Key tools help convert executable files into source code.
💥 Pwn: Pwn category starts with reverse engineering and continues with writing “malicious code” that causes a different program operation or server response, leading to server takeover and task completion.
📱 Mobile: Mobile applications deserve their own category. Most often, we deal with Android and iOS applications, which are disassembled and analyzed to understand their operation. The Mobile category is connected to Reversing and Web vulnerabilities. For tasks in this category, you will often need “rooted” phones or emulators.
🔓 Crypto: Cryptographic challenges require knowledge of cryptography and cryptographic algorithms. Breaking algorithms requires a great deal of persistence and creativity. Mathematicians and logicians have an advantage here. Writing code is also important.
🛠 Hardware: The Hardware category encompasses knowledge of the operation of electronic circuits, microcontrollers, and microprocessors. It also covers wireless technologies such as Bluetooth, radio signals, Wi-Fi, or other protocols.
🕵 OSINT: OSINT stands for open-source intelligence, and challenges in this category involve discovering publicly accessible information.
🧬 Forensics: Tasks that fall under the forensic category are usually extensive, as files such as hard disk copies, memory contents, etc., are often analyzed. You need to put yourself in the role of a detective searching for attackers’ traces.
In conclusion
Starting a career in this field may seem intimidating, but with the right approach and dedication, you can embark on the path to success. Focus on building a strong foundation in computing, getting involved in the cybersecurity community, acquiring knowledge on various platforms, participating in CTF competitions, and gaining practical experience.
For students, we also recommend attending summer schools or internships offered by companies during summer vacations. This way, you can familiarize yourself with the work in this field as much as possible.